A large-capacity zero-watermarking algorithm for color images based on combined transform domain
-
摘要:
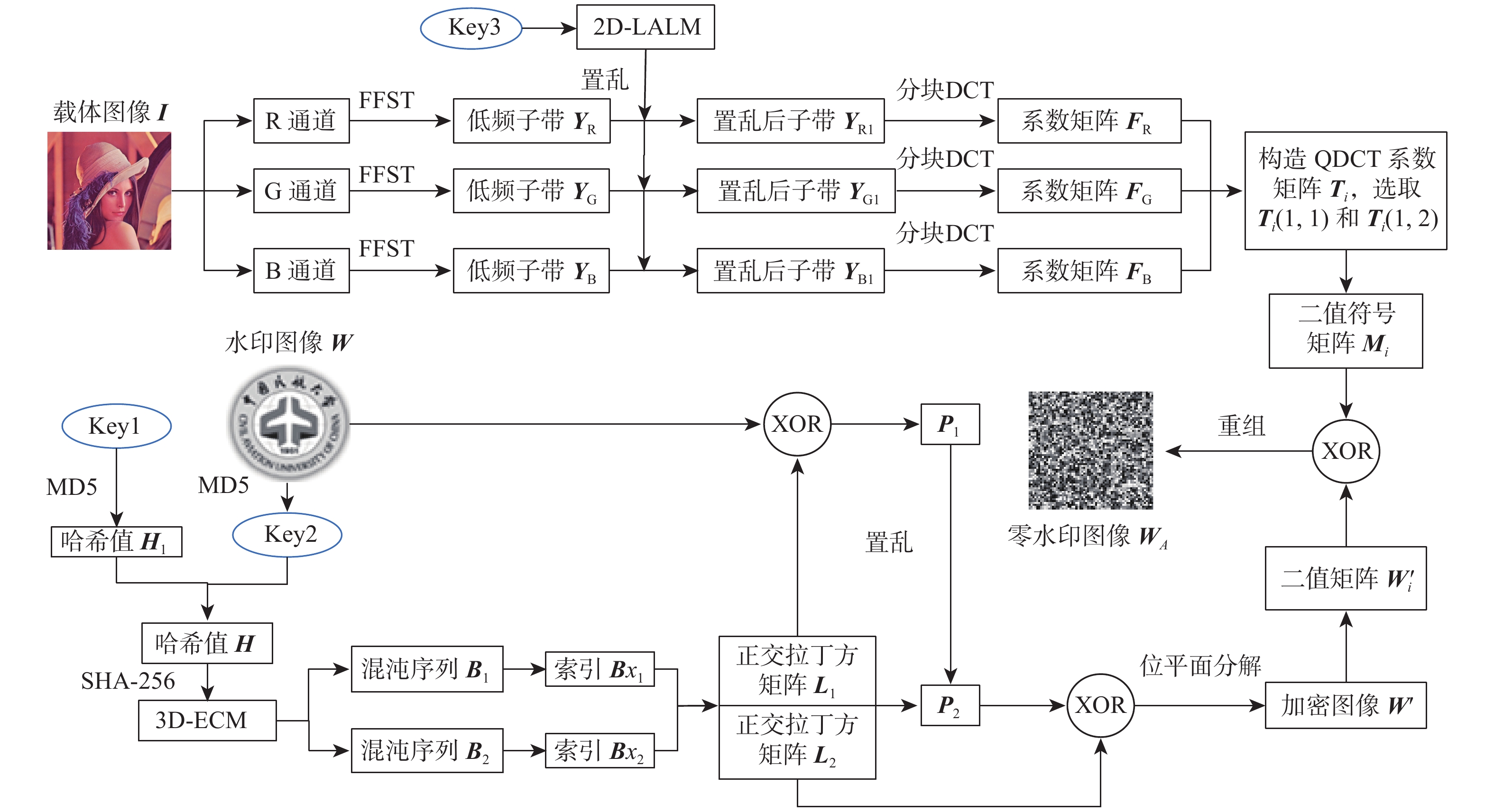
针对现有大多数彩色图像零水印方案中水印嵌入容量小且抗几何攻击鲁棒性能不佳等问题,提出一种基于组合变换域和位平面分解的大容量鲁棒零水印算法。对彩色载体图像的R、G、B通道分别进行快速有限剪切波变换(FFST),并对变换后的各低频子带进行非重叠分块置乱,将置乱后的各子带的分块离散余弦变换(DCT)系数用于构造四元数离散余弦变换(QDCT)系数矩阵;在每个QDCT系数矩阵中选取两个低频系数,利用其各个实部和虚部的符号极性构造8个二值鲁棒特征矩阵;将经过正交拉丁方置乱加密后的灰度水印图像按位分解,把位分解后的8个二值位平面分别与以上二值鲁棒特征矩阵进行异或并重组得到灰度级认证零水印。此外,在水印检测前,采用ORB算法对待认证图像进行几何校正。实验结果表明,所提算法水印嵌入容量和安全性高,且对于常规非几何攻击和几何攻击均具有较强的鲁棒性。
Abstract:In view of the small watermark embedding capacity and poor robustness against geometric attacks in most of the existing zero-watermarking schemes for color images, a robust zero-watermarking algorithm with a large capacity based on combined transform domain and bit-plane decomposition was proposed. Firstly, the R, G, and B channels of a color carrier image were respectively subjected to fast finite shearlet transform (FFST), and each low-frequency sub-band after FFST was processed by non-overlapping blocking and scrambling. The block discrete cosine transform (DCT) coefficients of each sub-band after the scrambling were used to construct the quaternion discrete cosine transform (QDCT) coefficient matrices, and then two low-frequency coefficients were selected from each QDCT coefficient matrix. Eight binary robust feature matrices were constructed according to the sign polarities of the real parts and the imaginary parts from the above two coefficients. Finally, the gray-level watermark image scrambled and encrypted by the orthogonal Latin squares matrices was decomposed by bits. The eight binary bit-planes after decomposition were used for XOR operation with the above binary robust feature matrices and recombined to obtain the final gray-level authentication zero-watermark. In addition, before the watermark detection, the image to be authenticated was geometrically corrected by the oriented FAST and rotated BRIEF (ORB) algorithm. The experimental results show that the proposed algorithm has high watermark embedding capacity and security, and it is highly robust to both conventional geometric and non-geometric attacks.
-
表 1 唯一性测试(NC值)
Table 1. Uniqueness test (NC值)
图像名称 Lena Baboon Peppers Sailboat House Mare Fiore Frog Lena 1.0000 0.5710 0.6210 0.5805 0.5825 0.5498 0.6893 0.5015 Baboon 0.5710 1.0000 0.6011 0.5712 0.6148 0.5173 0.5444 0.5928 Peppers 0.6210 0.6011 1.0000 0.6043 0.6313 0.5322 0.6075 0.5888 Sailboat 0.5805 0.5712 0.6043 1.0000 0.6122 0.5319 0.5773 0.5801 House 0.5825 0.6148 0.6313 0.6122 1.0000 0.5098 0.5192 0.6344 Mare 0.6572 0.5988 0.6529 0.6331 0.6091 1.0000 0.5863 0.5080 Fiore 0.6893 0.5444 0.6075 0.5773 0.5192 0.5863 1.0000 0.4525 Frog 0.5015 0.5928 0.5888 0.5801 0.6344 0.5080 0.4525 1.0000 表 2 常规攻击测试结果
Table 2. Test results of conventional attacks
攻击类型及强度 NC值 Lena Baboon Peppers Sailboat House Mare Fiore Frog 高斯噪声(0.1) 0.9810 0.9834 0.9890 0.9762 0.9695 0.9825 0.9747 0.9597 椒盐噪声(0.1) 0.9919 0.9897 0.9953 0.9840 0.9691 0.9907 0.9839 0.9657 中值滤波(5像素×5像素) 0.9982 0.9962 0.9991 0.9955 0.9945 0.9968 0.9961 0.9982 维纳滤波(5像素×5像素) 0.9992 0.9991 0.9998 0.9991 0.9988 0.9992 0.9994 0.9986 JPEG压缩(10) 0.9802 0.9825 0.9927 0.9761 0.9659 0.9846 0.9721 0.9733 JPEG2000压缩(90) 0.9965 0.9927 0.9973 0.9918 0.9836 0.9888 0.9958 0.9855 表 3 几何攻击测试结果
Table 3. Test results of geometric attacks
攻击类型及强度 NC值 Lena Baboon Peppers Sailboat House Mare Fiore Frog 旋转(10°) 0.9594 0.9877 0.9711 0.9746 0.9724 0.9763 0.9772 0.9566 旋转(90°) 0.9975 0.9992 0.9981 0.9975 0.9991 0.9995 0.9979 0.9943 缩小(0.5) 0.9938 0.9980 0.9988 0.9973 0.9947 0.9958 0.9920 0.9803 放大(2) 0.9960 0.9987 0.9972 0.9965 0.9969 0.9986 0.9951 0.9974 平移(向上10行) 0.9984 0.9967 0.9958 0.9935 0.9955 0.9966 0.9947 0.9882 平移(向左10列) 0.9687 0.9922 0.9897 0.9843 0.9851 0.9910 0.9890 0.9711 剪切(左上角1/16) 0.9722 0.9880 0.9808 0.9830 0.9758 0.9812 0.9808 0.9689 剪切(右上角1/16) 0.9826 0.9883 0.9869 0.9849 0.9797 0.9809 0.9772 0.9622 剪切(中心1/16) 0.9792 0.9846 0.9808 0.9810 0.9836 0.9905 0.9668 0.9728 表 4 组合攻击类型及参数
Table 4. Types and parameters of combined attacks
序号 攻击类型(参数) 1 高斯噪声(方差0.05)+平移攻击(右移10列) 2 椒盐噪声(强度0.05)+剪切攻击(左上角1/16) 3 维纳滤波(5像素×5像素)+旋转攻击(逆时针10°) 4 中值滤波(7像素×7像素)+JPEG2000压缩(Q=90) 5 JPEG压缩(Q=10)+剪切攻击(中心1/16) 6 剪切攻击(右下角1/16)+平移(上移10行) 表 5 组合攻击测试结果
Table 5. Test results of combined attacks
序号 攻击后图像 检测到水印图像(NC值) 1 

2 

3 

4 

5 

6 

表 6 FFST消融实验
Table 6. Ablation experiment of FFST
分解
层数平均NC值 高斯噪声 椒盐噪声 中值滤波 维纳滤波 JPEG压缩 0.8658 0.8714 0.9616 0.9720 0.9034 1 0.8677 0.8735 0.9654 0.9796 0.9039 2 0.8986 0.9067 0.9856 0.9950 0.9423 3 0.9669 0.9712 0.9961 0.9992 0.9876 表 7 ORB消融实验
Table 7. Ablation experiment of ORB
是否使用ORB 平均NC值 旋转 缩放 平移 否 0.8512 0.9979 0.9212 是 0.9633 0.9985 0.9855 表 8 本文算法与其他算法的鲁棒性对比测试结果
Table 8. Comparison of robustness between proposed algorithm and other algorithms
算法 NC值 高斯
噪声(0.05)高斯
噪声(0.1)椒盐
噪声(0.05)椒盐
噪声(0.1)中值滤波
(3像素×
3像素)中值滤波
(5像素×
5像素)维纳滤波
(3像素×
3像素)维纳滤波
(5像素×
5像素)JPEG
压缩(10)JPEG2000
压缩(90)旋转
(10°)旋转
(20°)文献[5] 0.9697 0.9533 0.9833 0.9736 0.9973 0.9946 0.9986 0.9967 0.9945 0.9878 0.7643 0.7059 文献[7] 0.8939 0.8735 0.9168 0.9085 0.9729 0.9580 0.9658 0.9614 0.8918 0.9413 0.8150 0.7992 文献[11] 0.9867 0.9707 0.9974 0.9813 0.9974 0.9974 1.0000 0.9974 0.9921 0.9921 1.0000 1.0000 文献[17] 0.8392 0.8038 0.8944 0.8590 0.9980 0.9834 0.9985 0.9818 0.9085 0.9279 0.8165 0.7794 文献[19] 0.9784 0.9978 0.9515 0.9964 0.9957 0.9970 0.9993 0.9989 0.9890 0.9926 0.6892 0.7520 文献[29] 0.9739 0.9574 0.9802 0.9728 0.9981 0.9949 0.9986 0.9964 0.9743 0.9911 0.8606 0.7616 文献[30] 0.9896 0.9929 1.0000 0.9958 1.0000 1.0000 1.0000 1.0000 0.9963 0.9988 0.9996 0.9996 本文算法 0.9857 0.9810 0.9943 0.9917 0.9990 0.9982 0.9998 0.9992 0.9806 0.9964 0.9595 0.9501 算法 NC值 平均
NC值旋转(40°) 缩小(0.5) 放大(2) 平移
(向上
10行)平移
(向下
10行)平移
(向左
10列)平移
(向右
10列)剪切
(左上角
1/16)剪切
(右上角
1/16)剪切
(左下角
1/16)剪切
(右下角
1/16)剪切
(中心
1/16)文献[5] 0.6855 0.9983 0.9995 0.9277 0.9196 0.8667 0.8845 0.9521 0.9476 0.9554 0.9480 0.9380 0.9309 文献[7] 0.7846 0.9738 0.9795 0.8658 0.8676 0.8631 0.8596 0.9677 0.9576 0.9558 0.9640 0.9560 0.9121 文献[11] 1.0000 1.0000 1.0000 0.8983 0.9153 0.8865 0.8604 0.9687 0.9707 0.9760 0.9761 0.9625 0.9723 文献[17] 0.7689 0.9935 0.9966 0.8450 0.8454 0.8465 0.7924 0.5934 0.7917 0.8606 0.7587 0.9567 0.8711 文献[19] 0.7912 0.9980 0.9992 0.9969 0.9865 0.9692 0.9105 0.8462 0.8338 0.8051 0.7632 0.8723 0.9228 文献[29] 0.5962 0.9989 0.9997 0.9273 0.9242 0.8677 0.8724 0.9523 0.9469 0.9541 0.9465 0.9353 0.9325 文献[30] 0.9992 1.0000 1.0000 0.9360 0.9685 0.8913 0.9470 0.8915 0.9362 0.9471 0.9251 0.8335 0.9694 本文算法 0.9524 0.9953 0.9970 0.9979 0.9966 0.9704 0.9785 0.9724 0.9825 0.9789 0.9780 0.9800 0.9839 表 9 水印容量对比结果
Table 9. Comparison of watermark capacity
-
[1] SHI H, LI Y N, HU B Y, et al. A robust and secure zero-watermarking copyright authentication scheme based on visual cryptography and block G-H feature[J]. Multimedia Tools and Applications, 2022, 81(26): 38019-38051. doi: 10.1007/s11042-022-13136-z [2] HAI T, LI C M, MOHAMAD ZAIN J, et al. Robust image watermarking theories and techniques: a review[J]. Journal of Applied Research and Technology, 2014, 12(1): 122-138. doi: 10.1016/S1665-6423(14)71612-8 [3] NIU P P, WANG L, WANG F, et al. Fast quaternion log-polar radial harmonic Fourier moments for color image zero-watermarking[J]. Journal of Mathematical Imaging and Vision, 2022, 64(5): 537-568. doi: 10.1007/s10851-022-01084-0 [4] 温泉, 孙锬锋, 王树勋. 零水印的概念与应用[J]. 电子学报, 2003, 31(2): 214-216. doi: 10.3321/j.issn:0372-2112.2003.02.015WEN Q, SUN T F, WANG S X. Concept and application of zero-watermark[J]. Acta Electronica Sinica, 2003, 31(2): 214-216(in Chinese). doi: 10.3321/j.issn:0372-2112.2003.02.015 [5] 熊祥光. 空域强鲁棒零水印方案[J]. 自动化学报, 2018, 44(1): 160-175.XIONG X G. A zero watermarking scheme with strong robustness in spatial domain[J]. Acta Automatica Sinica, 2018, 44(1): 160-175(in Chinese). [6] GHADI M, LAOUAMER L, NANA L, et al. A novel zero-watermarking approach of medical images based on Jacobian matrix model[J]. Security and Communication Networks, 2016, 9(18): 5203-5218. doi: 10.1002/sec.1690 [7] 赵彦霞, 王熙照. 基于SVD和DCNN的彩色图像多功能零水印算法[J]. 山东大学学报(工学版), 2018, 48(3): 25-33.ZHAO Y X, WANG X Z. Multipurpose zero watermarking algorithm for color image based on SVD and DCNN[J]. Journal of Shandong University (Engineering Science), 2018, 48(3): 25-33(in Chinese). [8] JIANG F F, GAO T G, LI D. A robust zero-watermarking algorithm for color image based on tensor mode expansion[J]. Multimedia Tools and Applications, 2020, 79(11): 7599-7614. [9] 吴德阳, 赵静, 汪国平, 等. 一种基于改进奇异值和子块映射的图像零水印技术[J]. 光学学报, 2020, 40(20): 2010002. doi: 10.3788/AOS202040.2010002WU D Y, ZHAO J, WANG G P, et al. An image zero watermarking technology based on ameliorated singular value and subblock mapping[J]. Acta Optica Sinica, 2020, 40(20): 2010002(in Chinese). doi: 10.3788/AOS202040.2010002 [10] 张天骐, 叶绍鹏, 刘鉴兴, 等. 基于彩色图像Tetrolet变换的频数质心零水印算法[J]. 系统工程与电子技术, 2023, 45(1): 41-48.ZHANG T Q, YE S P, LIU J X, et al. Frequency centroid zero watermarking algorithm based on Tetrolet transform of color image[J]. Systems Engineering and Electronics, 2023, 45(1): 41-48(in Chinese). [11] XIA Z Q, WANG X Y, WANG C P, et al. Novel quaternion polar complex exponential transform and its application in color image zero-watermarking[J]. Digital Signal Processing, 2021, 116: 103130. doi: 10.1016/j.dsp.2021.103130 [12] CHEN S Y, SU Q T, SUN Y H, et al. A blind color image watermarking algorithm using the energy concentration principle of Hadamard matrix[J]. Optik, 2022, 249: 168231. doi: 10.1016/j.ijleo.2021.168231 [13] SU Q T, LIU D C, SUN Y H. A robust adaptive blind color image watermarking for resisting geometric attacks[J]. Information Sciences, 2022, 606: 194-212. doi: 10.1016/j.ins.2022.05.046 [14] 叶绍鹏, 张天骐, 柏浩钧, 等. 基于Baker映射与时空混沌相结合的CT-QR域双彩色鲁棒盲水印算法[J]. 信号处理, 2021, 37(5): 843-853.YE S P, ZHANG T Q, BAI H J, et al. Dual-color robust blind watermarking algorithm in CT-QR domain based on baker map and spatio-temporal chaos[J]. Journal of Signal Processing, 2021, 37(5): 843-853(in Chinese). [15] 刘得成, 苏庆堂, 袁子涵, 等. 结合汉明码和图像矫正的彩色图像盲水印[J]. 中国图象图形学报, 2021, 26(5): 1138-1146. doi: 10.11834/jig.200384LIU D C, SU Q T, YUAN Z H, et al. Blind color image watermarking method combining Hamming code with image correction[J]. Journal of Image and Graphics, 2021, 26(5): 1138-1146(in Chinese). doi: 10.11834/jig.200384 [16] WANG K S, GAO T G, YOU D T, et al. A secure dual-color image watermarking scheme based 2D DWT, SVD and Chaotic map[J]. Multimedia Tools and Applications, 2022, 81(5): 6159-6190. doi: 10.1007/s11042-021-11725-y [17] ABDULRAHMAN A K, OZTURK S. A novel hybrid DCT and DWT based robust watermarking algorithm for color images[J]. Multimedia Tools and Applications, 2019, 78(12): 17027-17049. [18] 胡森, 吴德阳, 仲美玉, 等. 基于SURF和半色调映射加密的彩色零水印算法[J]. 激光与光电子学进展, 2021, 58(20): 2010017.HU S, WU D Y, ZHONG M Y, et al. Color zero-watermarking algorithm based on SURF and halftone mapping encryption[J]. Laser & Optoelectronics Progress, 2021, 58(20): 2010017(in Chinese). [19] WU D Y, WANG M M, ZHAO J, et al. Color zero-watermarking algorithm for medical images based on BEMD-schur decomposition and color visual cryptography[J]. Security and Communication Networks, 2021, 2021: 7081194. [20] RUBLEE E, RABAUD V, KONOLIGE K, et al. ORB: an efficient alternative to SIFT or SURF[C]// 2011 International Conference on Computer Vision. Piscataway: IEEE Press, 2011: 2564-2571. [21] HAMILTON W R, HAMILTON W E, EVERETT J D, et al. Elements of quaternions[M]. London: Longmans, Green, & co. , 1866. [22] FENG W, HU B. Quaternion discrete cosine transform and its application in color template matching[C]// 2008 Congress on Image and Signal Processing. Piscataway: IEEE Press, 2008: 252-256. [23] 崔滨. 融合四元数视觉特征的彩色图像水印算法研究[D]. 济南: 山东师范大学, 2021: 9-11.CUI B. Research on color image watermarking algorithm with quaternion visual features[D]. Jinan: Shandong Normal University, 2021: 9-11(in Chinese). [24] HÄUSER S, STEIDL G. Convex multiclass segmentation with shearlet regularization[J]. International Journal of Computer Mathematics, 2013, 90(1): 62-81. doi: 10.1080/00207160.2012.688960 [25] TAN L, YU X. Medical image fusion based on fast finite shearlet transform and sparse representation[J]. Computational and Mathematical Methods in Medicine, 2019, 2019: 3503267. [26] LIU H J, WANG X Y, KADIR A. Constructing chaos-based hash function via parallel impulse perturbation[J]. Soft Computing, 2021, 25(16): 11077-11086. doi: 10.1007/s00500-021-05849-4 [27] University of Granada, Computer Vision Group (2002) CVG-UGR Image Database[EB/OL]. (2014-03-13)[2022-04-23] http://decsai.ugr.es/cvg/dbimagenes/c512.php. [28] 胡坤, 李聪, 胡建平, 等. 基于BEMD与DCT的彩色图像多重水印鲁棒算法[J]. 北京航空航天大学学报, 2023, 49(1): 165-176.HU K, LI C, HU J P, et al. Robust multiple watermarking algorithm for color image via BEMD and DCT[J]. Journal of Beijing University of Aeronautics and Astronautics, 2023, 49(1): 165-176(in Chinese). [29] KANG X B, LIN G F, CHEN Y J, et al. Robust and secure zero-watermarking algorithm for color images based on majority voting pattern and hyper-chaotic encryption[J]. Multimedia Tools and Applications, 2020, 79(1): 1169-1202. [30] YANG H Y, QI S R, NIU P P, et al. Color image zero-watermarking based on fast quaternion generic polar complex exponential transform[J]. Signal Processing: Image Communication, 2020, 82: 115747. doi: 10.1016/j.image.2019.115747 -







 下载:
下载: