Security handover authentication scheme for high-speed railway symbiotic network based on NTRU lattice
-
摘要:
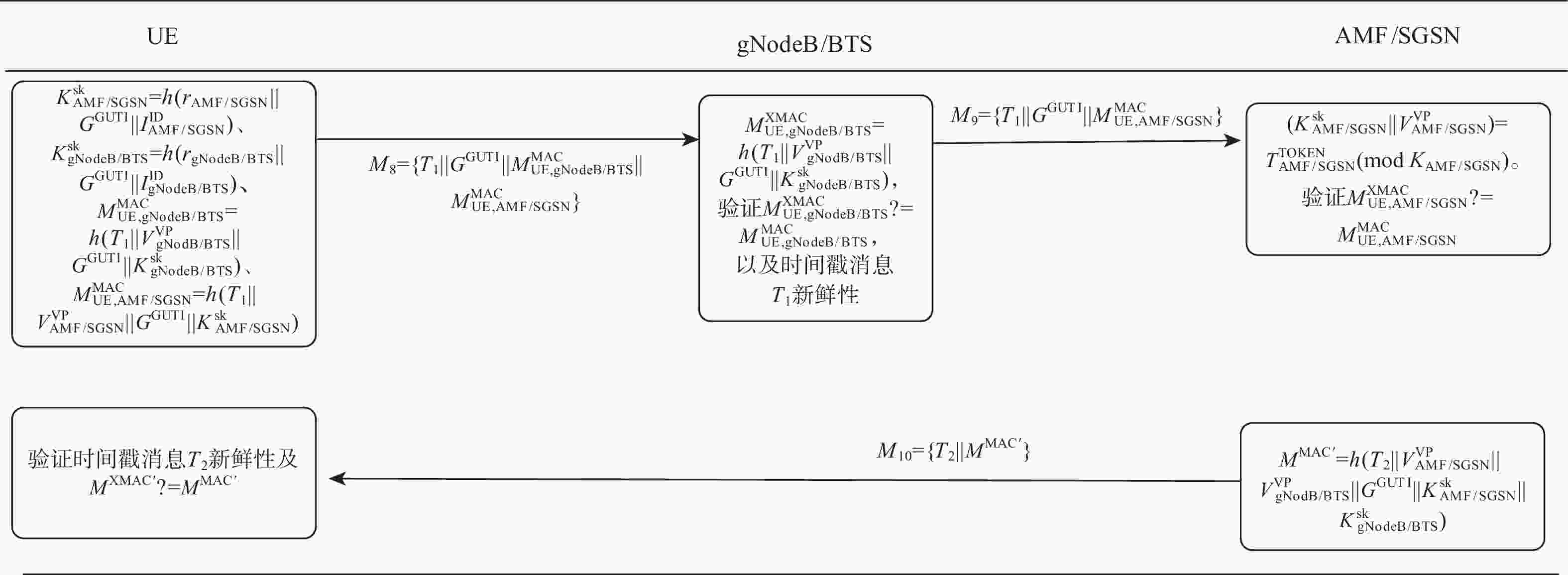
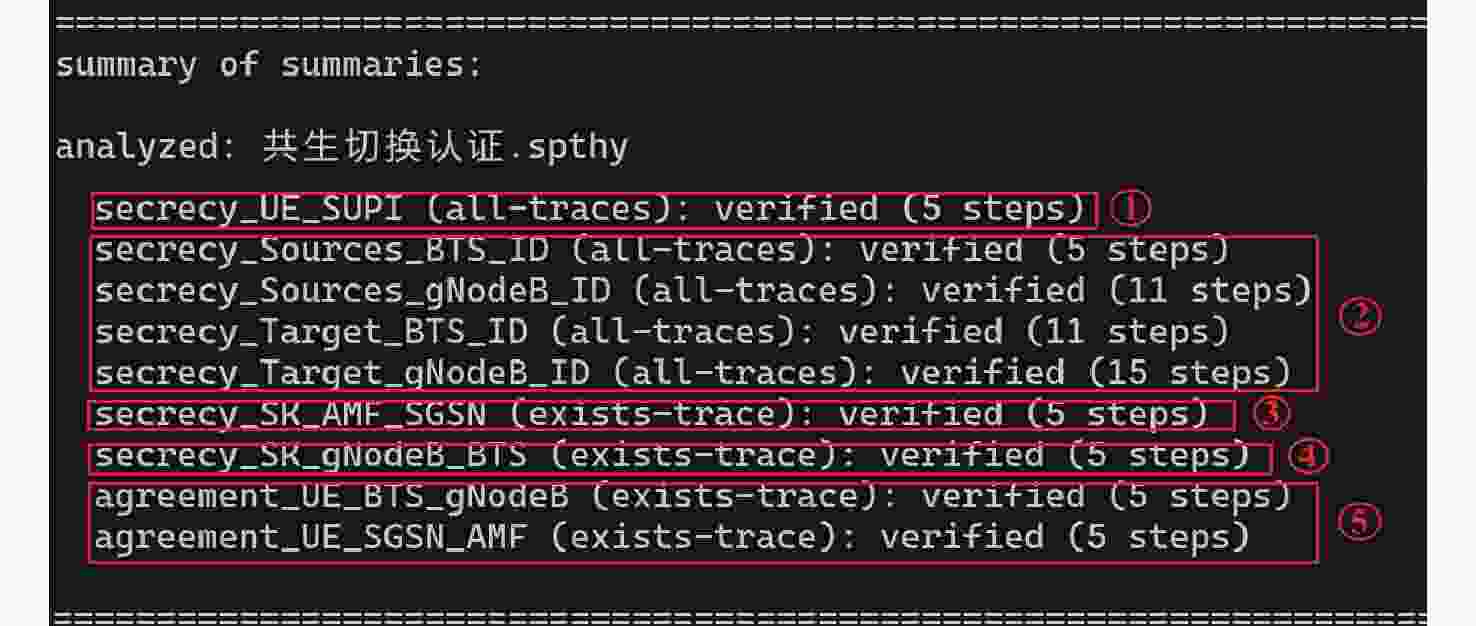
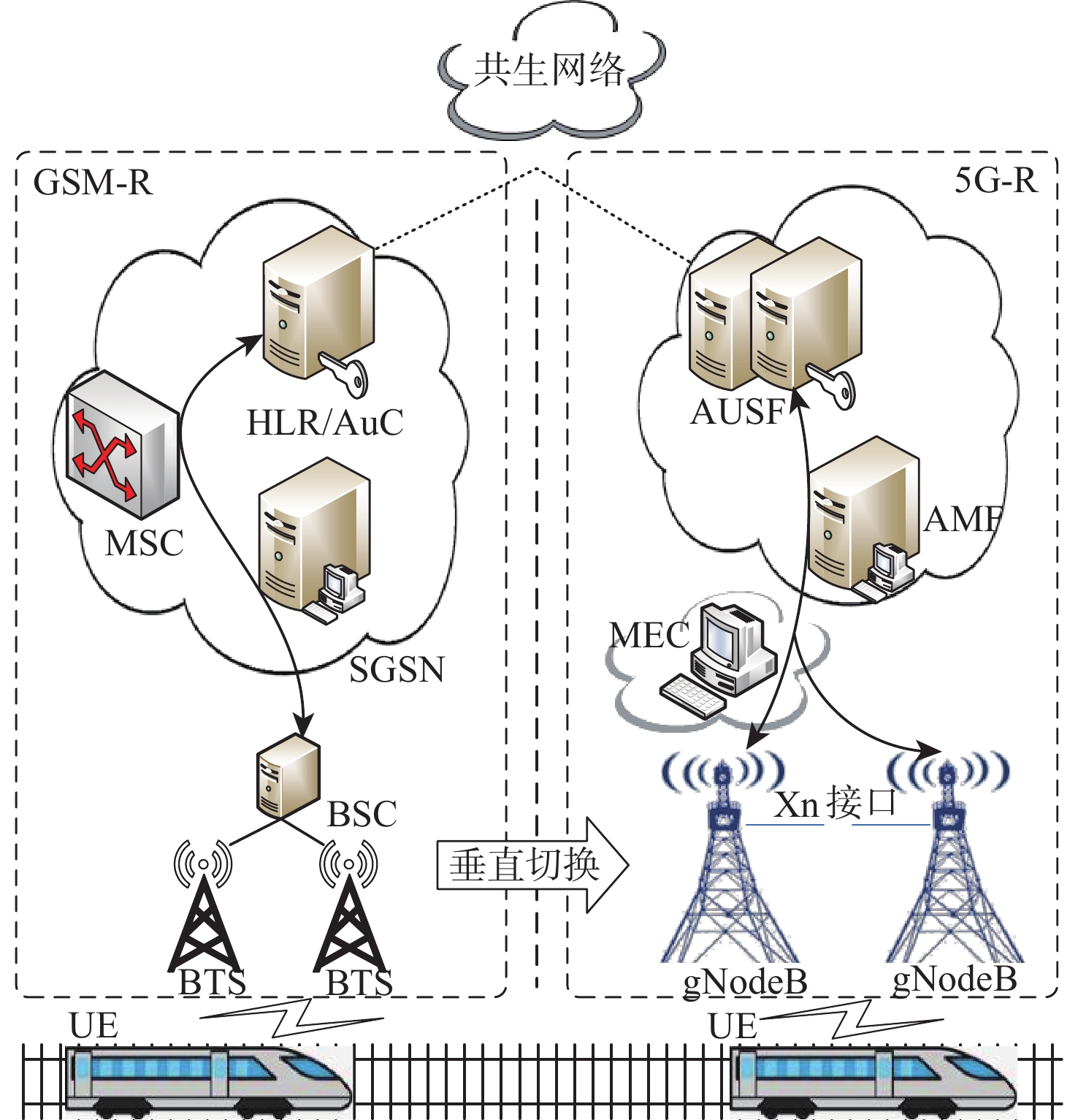
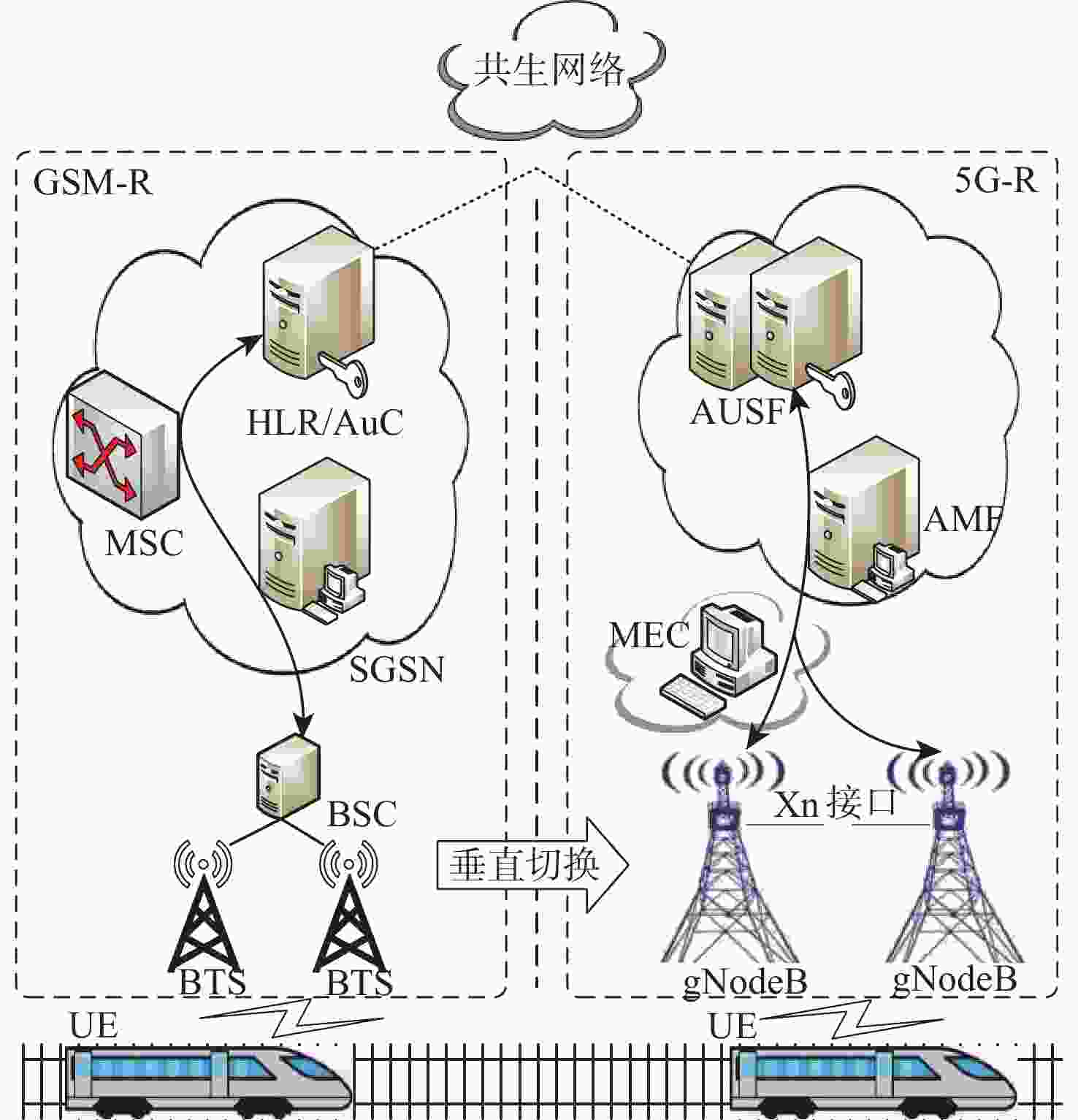
针对高铁GSM-R无线通信系统向下一代5G-R网络演进过程中,共生网络垂直切换时存在身份泄露、不具备前后向安全性和认证开销大等问题,提出了一种基于NTRU格上的高铁共生网络安全切换认证方案。设计了基于NTRU格的双向认证机制,克服了身份信息SUPI明文传输易泄露的缺点;提出基于共享密钥的哈希链加密方法,设计共享密钥生成和共生网络切换令牌策略,实现切换认证密钥的预生成,确保了共享密钥的动态更新及前后向安全性;采用中国剩余定理及时间戳机制实现了会话密钥的机密性,完成了共生网络的切换认证。通过BAN逻辑形式化理论证明和TAMARIN协议仿真验证工具对所提方法进行安全性分析,结果表明:与同类方法相比,所提方法确保了身份的匿名性和密钥前后向安全性,可有效抵抗DoS攻击和中间人攻击等攻击,具有更低的切换开销,能够满足高铁共生网络安全无缝切换认证的需求。
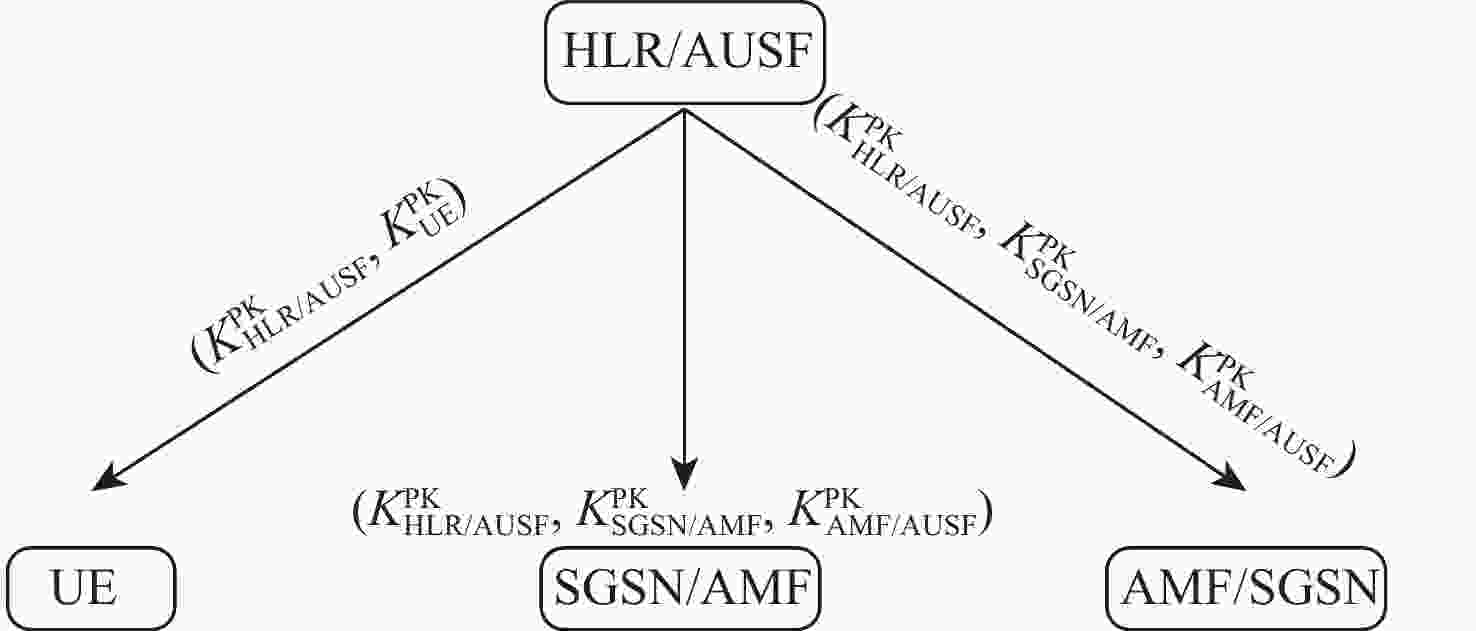
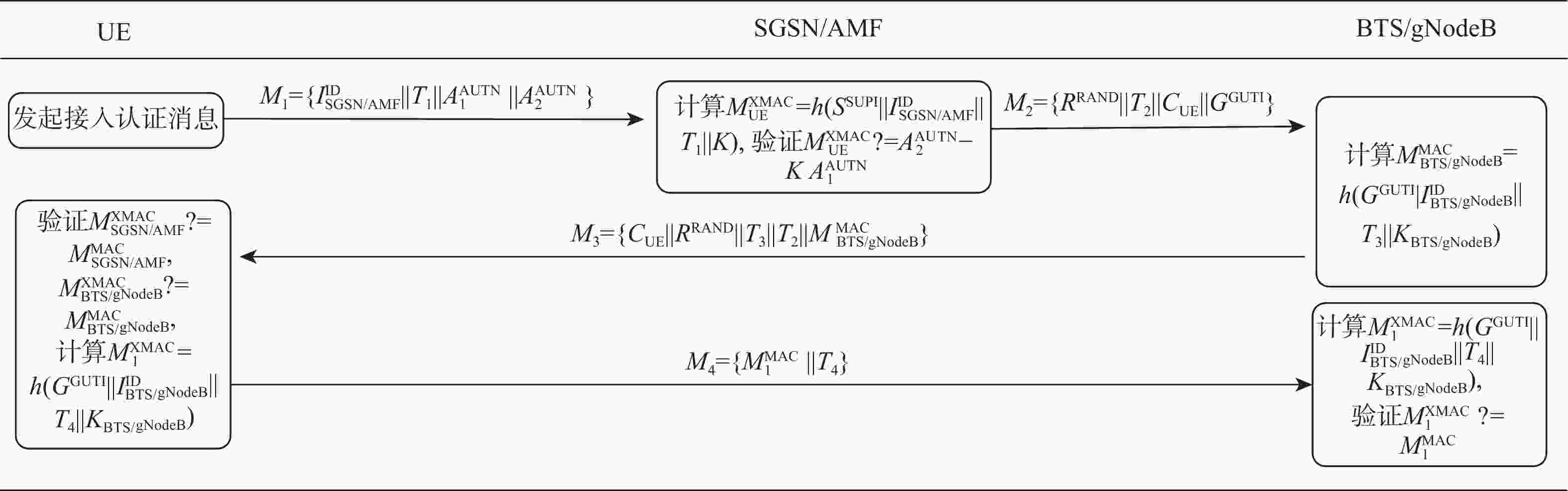
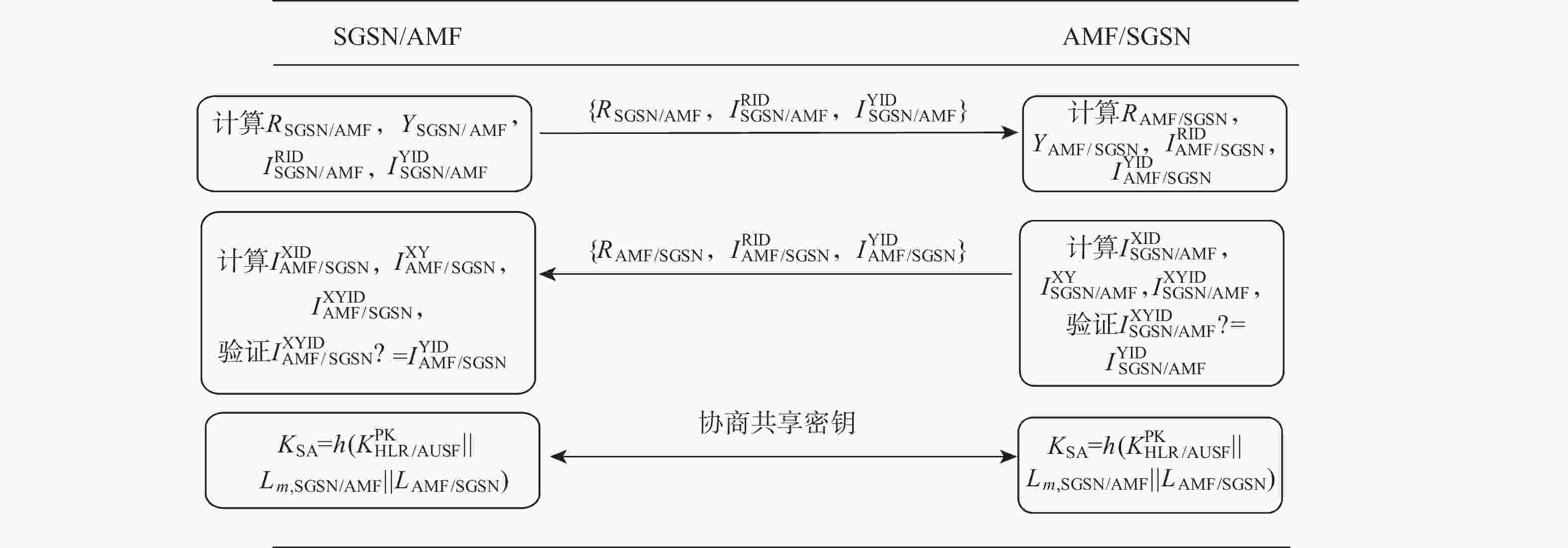
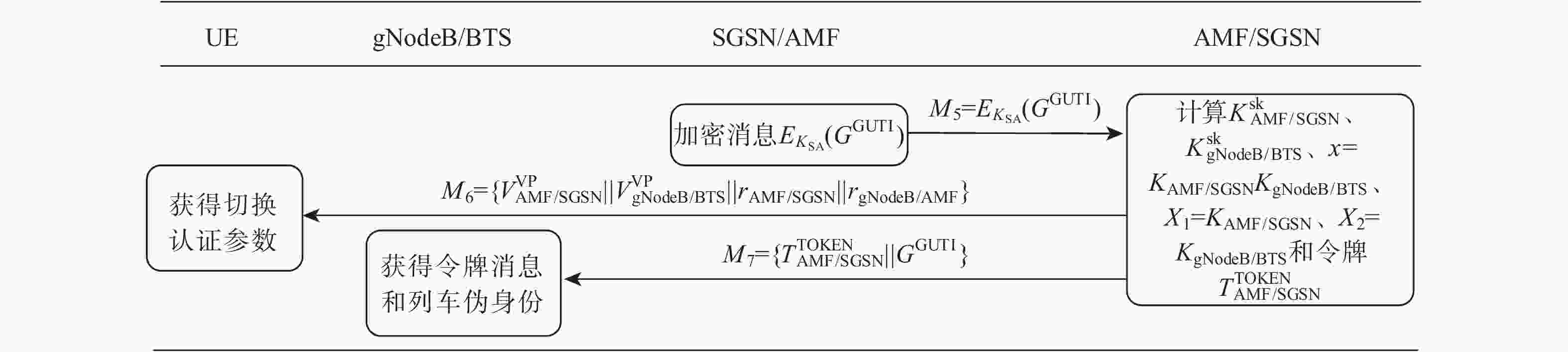
Abstract:A high-speed railway symbiotic network security handover authentication scheme based on NTRU lattice is proposed to address the issues of identity leakage, lack of forward and backward security, and high authentication overhead during the evolution of the high-speed railway GSM-R wireless communication system to the next generation 5G-R network during vertical handover. Firstly, a bidirectional authentication mechanism based on NTRU lattice was designed to overcome the vulnerability of identity information SUPI plaintext transmission to leakage. Second, a shared key-based hash chain encryption technique is suggested. To accomplish pre-creation of handover authentication keys, shared key generation and symbiotic network switching token strategies are created, guaranteeing dynamic updates of shared keys and forward and backward security. Then, using the Chinese remainder theorem and timestamp mechanism, the confidentiality of the session key was achieved, and the handover authentication of the symbiotic network was completed. Finally, the security of the proposed method was analyzed using BAN logic theory and TAMARIN protocol simulation verification tools. The findings demonstrate that, in comparison to comparable techniques, the suggested approach guarantees identity anonymity and forward and backward key security, can successfully fend off DoS and man-in-the-middle attacks, has lower switching costs, and can satisfy the demands of seamless handover authentication for high-speed rail symbiotic network security.
-
表 1 安全性能对比
Table 1. Safety performance comparison
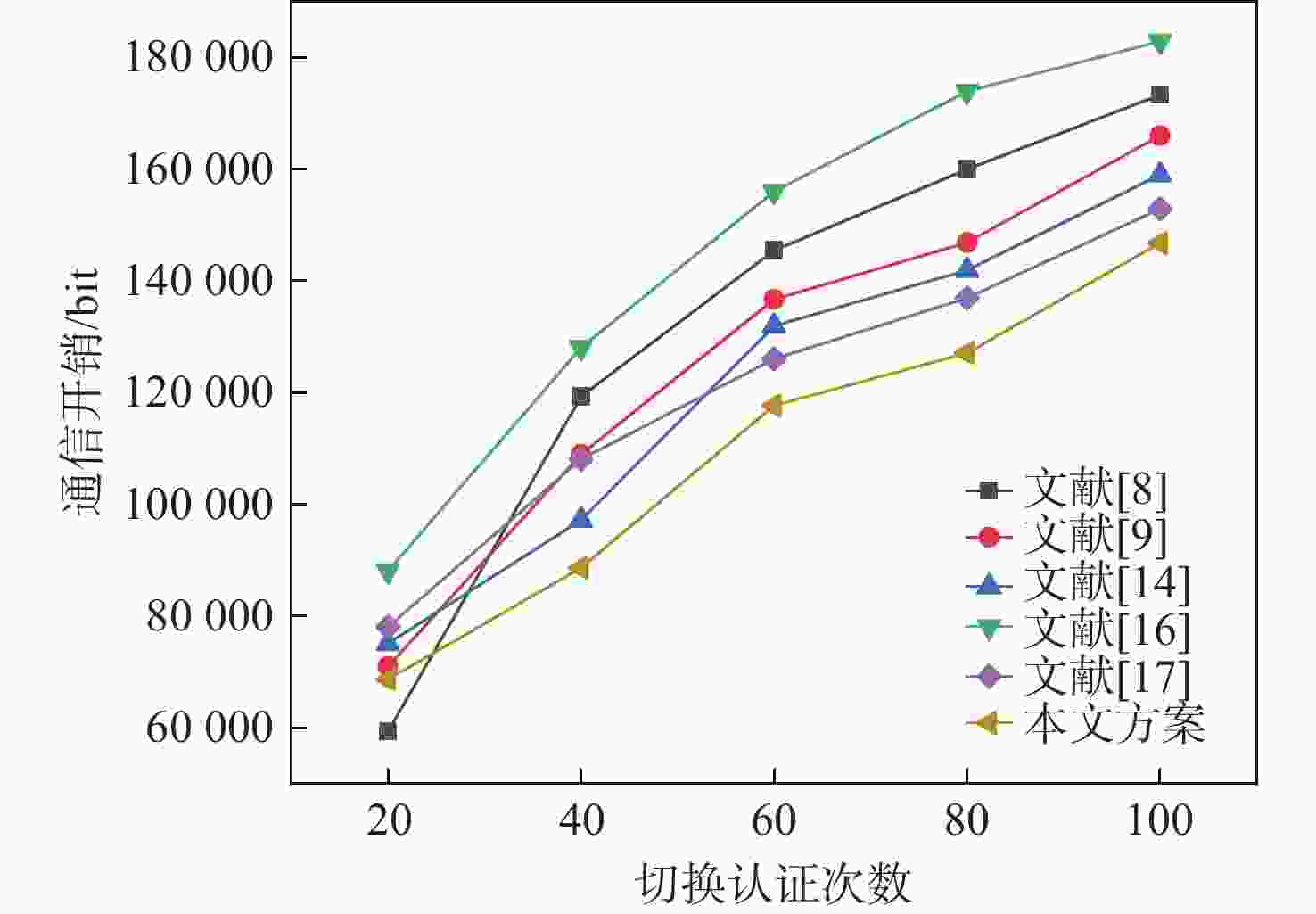
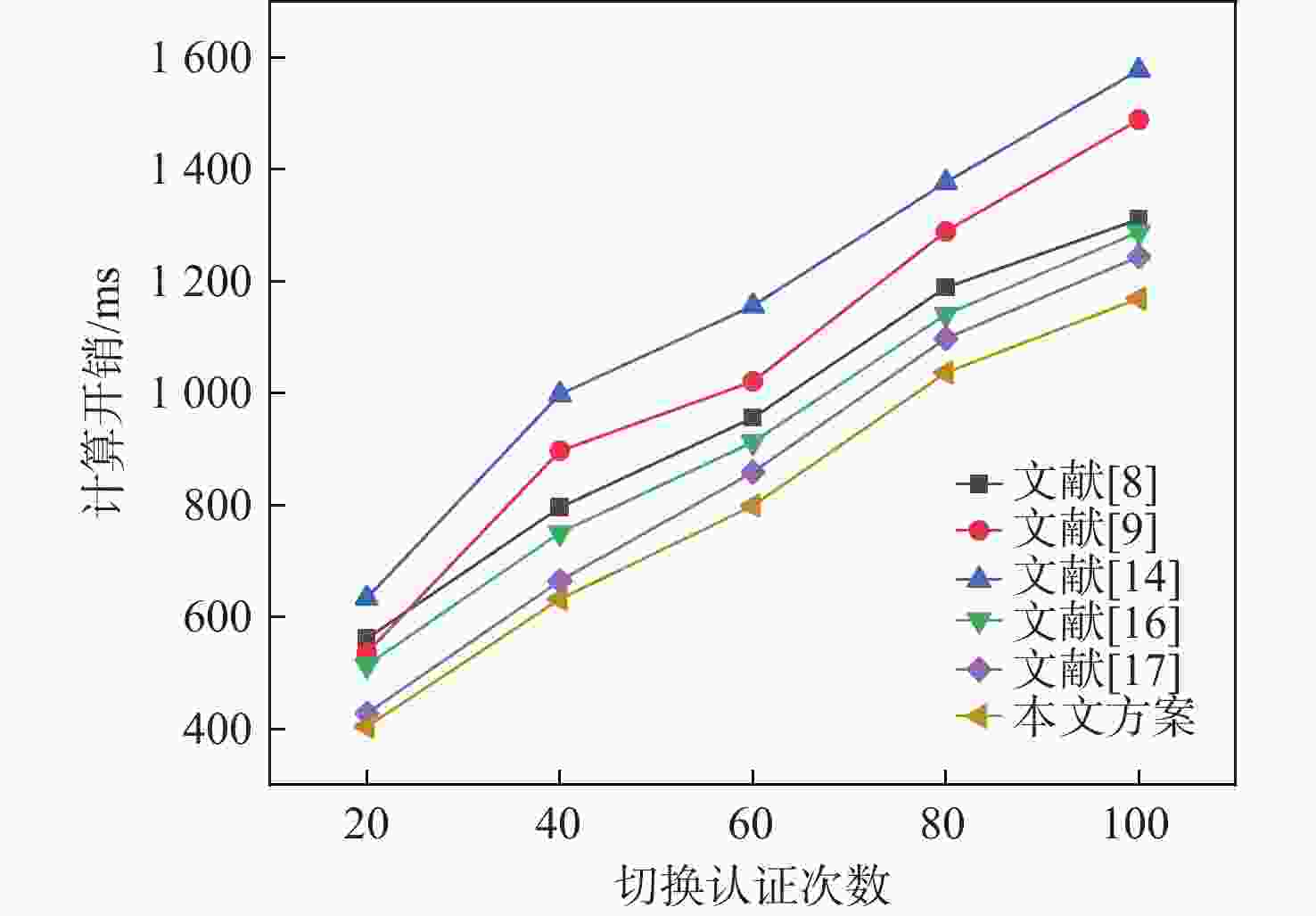
表 2 通信开销及计算开销对比
Table 2. Comparison of communication overhead and computing overhead
方案 UE通信量/bit 核心网通信量/bit 总通信量/bit 预认证耗时/ms 切换认证耗时/ms 总耗时/ms 文献[8] 863 2302 2965 15THASH+7TS+TM≈15.4 15THASH+7TS+TM≈12.7 28.1 文献[9] 960 2588 3548 5THASH+7TA+TM+8TECC≈26.8 26.8 文献[14] 1102 2652 3754 8THASH+5TA+3TM+9TECC≈31.7 31.7 文献[16] 1263 2897 4160 4THASH+3TA+TM+7TECC≈24.5 24.5 文献[17] 974 2929 3903 5THASH+TNE+TND+TNM≈11.6 9THASH+2TNE+2TND+TNM≈9.8 21.4 本文方案 765 2667 3432 4THASH+3TNE+2TND+2TNM≈12.8 7THASH+2TNM≈7.4 20.2 -
[1] 陈永, 刘雯, 詹芝贤. 基于混合密钥增强的LTE-R车地认证密钥协商方案[J]. 铁道学报, 2023, 45(6): 69-79.CHEN Y, LIU W, ZHAN Z X. A train-to-ground authentication key agreement enhanced scheme based on hybrid secrurity key for LTE-R[J]. Journal of the China Railway Society, 2023, 45(6): 69-79(in Chinese). [2] HE R S, AI B, ZHONG Z D, et al. 5G for railways: next generation railway dedicated communications[J]. IEEE Communications Magazine, 2022, 60(12): 130-136. [3] 张馨丹, 李辉, 郭强亮. 5G-R和GSM-R网络列车调度通信业务平滑过渡方案研究[J]. 铁道标准设计, 2022, 66(10): 166-172.ZHANG X D, LI H, GUO Q L. Research on smooth transition scheme of 5G-R and GSM-R network train dispatching communication services[J]. Railway Standard Design, 2022, 66(10): 166-172 (in Chinese). [4] 陈永, 康婕, 陶瑄. 改进5G-R自适应高速铁路越区切换算法[J]. 北京航空航天大学学报, 2025, 51(3): 724-731.CHEN Y, KANG J, TAO X. An improved 5G-R adaptive high-speed railway handover algorithm[J]. Journal of Beijing University of Aeronautics and Astronautics, 2025, 51(3): 724-731(in Chinese). [5] TANG Q, ERMIS O, NGUYEN C D, et al. A systematic analysis of 5G networks with a focus on 5G core security[J]. IEEE Access, 2022, 10: 18298-18319. [6] SUN B, GUO Y, YU Y J, et al. Reliability analysis of CTCS-3 train-ground communication system based on 5G-R[J]. IEEE Transactions on Vehicular Technology, 2023, 72(10): 12927-12940. [7] WANG Y, ZHANG W F, WANG X M, et al. Improving the security of LTE-R for high-speed railway: from the access authentication view[J]. IEEE Transactions on Intelligent Transportation Systems, 2022, 23(2): 1332-1346. [8] CAO J, MA M D, FU Y L, et al. CPPHA: capability-based privacy-protection handover authentication mechanism for SDN-based 5G HetNets[J]. IEEE Transactions on Dependable and Secure Computing, 2021, 18(3): 1182-1195. [9] ALEZABI K A, HASHIM F, HASHIM S J, et al. Efficient authentication and re-authentication protocols for 4G/5G heterogeneous networks[J]. EURASIP Journal on Wireless Communications and Networking, 2020, 2020: 105. [10] MA T, HU F. A cross-layer collaborative handover authentication approach for 5G heterogeneous network[J]. Journal of Physics: Conference Series, 2019, 1169: 012066. [11] YANG J, JI X S, HUANG K Z, et al. Unified and fast handover authentication based on link signatures in 5G SDN-based HetNet[J]. IET Communications, 2019, 13(2): 144-152. [12] CUI Q M, ZHU Z B, NI W, et al. Edge-intelligence-empowered, unified authentication and trust evaluation for heterogeneous beyond 5G systems[J]. IEEE Wireless Communications, 2021, 28(2): 78-85. [13] KALIA P, KUMAR A. 5G enabled universal seamless HO authentication in heterogeneous networks[C]//Proceedings of the 2nd International Conference on Advanced Technologies in Intelligent Control, Environment, Computing & Communication Engineering. Piscataway: IEEE Press, 2022: 1-5. [14] LIU Y B, HUO L J, WU J, et al. MRSA: mask random array protocol for efficient secure handover authentication in 5G HetNets[J]. IEEE Transactions on Dependable and Secure Computing, 2023, 20(5): 3809-3827. [15] DIVAKARAN J, CHAKRAPANI A, SRIHARI K. Fuzzy logic based handover authentication in 5G telecommunication heterogeneous networks[J]. Computer Systems Science and Engineering, 2023, 46(1): 1141-1152. [16] SHARMA V, YOU I, LEU F Y, et al. Secure and efficient protocol for fast handover in 5G mobile Xhaul networks[J]. Journal of Network and Computer Applications, 2018, 102: 38-57. [17] ZHOU Y S, WANG L A. A lattice-based authentication scheme for roaming service in ubiquitous networks with anonymity[J]. Security and Communication Networks, 2020, 2020: 2637916. [18] 李瑞琪, 贾春福, 王雅飞. 基于NTRU的多密钥同态代理重加密方案及其应用[J]. 通信学报, 2021, 42(3): 11-22.LI R Q, JIA C F, WANG Y F. Multi-key homomorphic proxy re-encryption scheme based on NTRU and its application[J]. Journal on Communications, 2021, 42(3): 11-22(in Chinese). [19] ABDEL-MALEK M A, AKKAYA K, BHUYAN A, et al. A proxy signature-based swarm drone authentication with leader selection in 5G networks[J]. IEEE Access, 2022, 10: 57485-57498. [20] CORTIER V, DELAUNE S, DREIER J, et al. Automatic generation of sources lemmas in tamarin: towards automatic proofs of security protocols[J]. Journal of Computer Security, 2022, 30(4): 573-598. [21] RAM S B, ODELU V. Security analysis of a key exchange protocol under Dolev-Yao threat model using tamarin prover[C]//Proceedings of the IEEE 12th Annual Computing and Communication Workshop and Conference. Piscataway: IEEE Press, 2022: 667-672. -






 下载:
下载: